Table of Contents
Summary
Modern ransomware isn’t just encryption. Today’s attacks combine data theft, DDoS, and executive pressure into a coordinated four-layer extortion model — and they move fast. Attacks surged 47% in 2025, the full attack chain now compresses to hours, and 96% of cases include data theft.
Ransomware has a branding problem. Most people still picture it as a single event: files get encrypted; a ransom note appears, you pay (or you don’t), and it’s over.
That version of ransomware hasn’t been the dominant threat for years.
Today’s ransomware operators run a four-layer extortion model. They’ve had time to study your defenses, copy your data, and line up multiple pressure campaigns before you even know you’ve been hit. Publicly reported ransomware attacks reached 7,200 in 2025, a 47% jump over 2024, according to Recorded Future. The playbook is working. And it’s getting more calculated every quarter.
This post breaks down exactly how multi-extortion ransomware works, layer by layer, so your team can defend against the actual threat and not the simplified version that lives in vendor slide decks.
What Is Multi-Extortion Ransomware?
Multi-extortion ransomware is an attack model that uses multiple pressure tactics to maximize the probability that a victim pays. Where early ransomware relied entirely on encryption to force a ransom, modern attacks fold in data theft, public leak threats, and distributed denial-of-service attacks to create pressure from multiple directions at once.
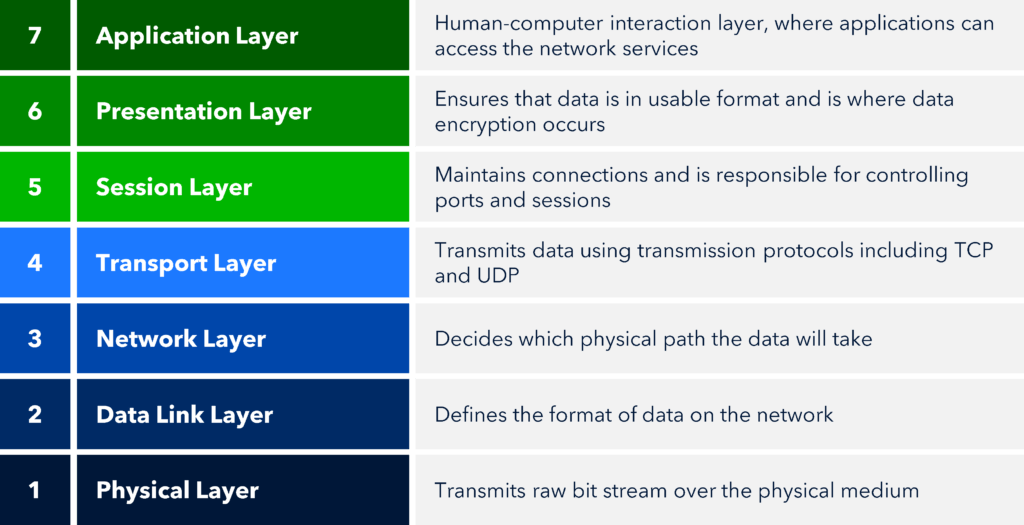
The evolution went roughly like this:
Single extortion: Encrypt data. Demand payment for the decryption key.
Double extortion: Encrypt data and steal it. Demand payment, or the stolen data gets published on a public leak site.
Triple extortion: Add a DDoS attack to the mix. Now the target is dealing with encrypted systems, a leak threat, and a network availability problem at the same time.
Quadruple extortion: Go after individuals. Executives, customers, employees. Anyone whose personal exposure creates additional pressure on the organization to pay.
One thing worth stating before going further: these layers don’t always execute in a clean linear sequence. Attackers adapt based on victim response. A DDoS attack might launch at the same time as encryption, or a leak threat might come before any data is encrypted at all. The model below describes the architecture of a full-scale attack, not a guarantee that every step follows a fixed script.
The 4-Layer Attack Model
Layer 1: Initial Access and Dwell Time
The most dangerous part of a ransomware attack is the part you don’t see.
After gaining initial access, threat actors don’t immediately detonate. They move laterally using legitimate tools like PowerShell and RDP, specifically because these generate less noise than purpose-built malware. The goal at this stage is access, not disruption. They’re mapping the environment, identifying high-value data, and positioning for maximum impact.
Breakout times, meaning the window between initial access and lateral movement, have compressed dramatically. According to research from Maveris Labs, average breakout times are now down to 48 minutes, with extreme cases clocking in at 51 seconds.
Once inside, attackers don’t rush. Sophos data shows the median dwell time for ransomware cases in 2025 has dropped to just 4 days. That’s still four days of unauthorized access before detection. According to ThreatDown by Malwarebytes, the full attack chain from initial access through lateral movement, data exfiltration, and encryption has compressed from weeks to hours.
If you’re relying on detection after the fact, you’re already behind.
Layer 2: Encryption
Encryption used to be the main event. It’s increasingly becoming optional.
According to Sophos’s State of Ransomware 2025 report, the encryption rate has dropped to its lowest point in six years, from 70% in 2024 to 50% in 2025. At the same time, the share of extortion attacks that skip encryption entirely has doubled, from 3% to 6%.
Attackers are learning that they don’t need to encrypt anything if the threat of a data leak is enough. Why risk triggering endpoint detection from encryption activity when the stolen data already gives you leverage?
That said, encryption remains a central tactic in most multi-extortion campaigns. The original ransomware model relied on a single vector: encrypt data and demand payment for the decryption key. Double extortion added data theft as a second vector. Refusing the ransom just means the stolen data gets published instead.
The implication for defenders is straightforward: backup-and-restore is no longer a complete answer. If your data has already been exfiltrated, restoring from backup doesn’t eliminate the threat.
Layer 3: Leak Sites and Data Exfiltration
Data theft isn’t a secondary feature of modern ransomware. It’s standard.
According to Cyberhaven research, 96% of ransomware cases investigated included data theft. That’s essentially universal. The double extortion model has become the default, not the exception.
Once data is exfiltrated, it gets held as leverage. Vectra AI notes that stolen data is typically published on a threat actor’s leak site after a deadline expires, often released in stages to maintain pressure over time. Release some data to prove the threat is real, hold the rest to keep the victim negotiating.
The infrastructure supporting this model is growing fast. Recorded Future identified over 56 new leak sites in 2024, more than double the previous year’s count. In just the first half of 2025, over 3,700 victims were listed on leak sites, a 67% increase year-over-year.
This isn’t a niche tactic anymore. It’s an industry.
Layer 4: DDoS
If encryption creates business disruption and a leak site creates reputational pressure, a DDoS attack creates operational emergency. And emergency creates urgency to pay.
That’s the logic. Layer a volumetric network attack on top of an already compromised, partially encrypted environment and you’ve got a team trying to respond to three crises at once with a fraction of their normal capacity.
As BlackFog documents, triple extortion adds DDoS to the attack stack, and quadruple extortion goes further by directly pressuring executives, customers, or other stakeholders who have their own reasons to want the situation resolved fast.
What makes this hard to defend against is how accessible the capability has become. Vectra AI notes that some ransomware-as-a-service operators now bundle DDoS capabilities as an affiliate service, putting multi-extortion attacks within reach of threat actors who couldn’t build that infrastructure themselves.
Recorded Future recommends that organizations ensure their DDoS mitigation strategies account for attacks that accompany ransomware incidents. The threat isn’t theoretical. It’s a documented feature of how modern extortion campaigns operate.
Why Traditional Defenses Fall Short
Most security stacks were built to respond to one problem at a time. A malware alert. A phishing attempt. A DDoS event.
Multi-extortion ransomware is designed to overwhelm a response team by triggering multiple crises across different domains at once: endpoint security, data governance, network availability, and executive communications. The pressure isn’t just technical. It’s psychological. And it’s coordinated.
Defending against this model requires a few specific things.
Continuous network visibility. If attackers are spending days inside your environment before detonating, you need behavioral anomaly detection that catches lateral movement early, not signature-based detection that only fires when something known happens.
DDoS mitigation that’s always on. A DDoS attack triggered mid-incident isn’t the time to activate an on-demand scrubbing service. Sub-second automated mitigation matters precisely because the attack is designed to land while your team is already overwhelmed.
Data exfiltration monitoring. Given that 96% of ransomware cases now include data theft, detecting unusual outbound data movement before encryption happens is a critical intervention point.
Incident response that accounts for multi-vector pressure. Your playbook needs to address all four layers, not just endpoint recovery and backup restoration.
The Bottom Line
Multi-extortion ransomware isn’t just a more complex version of the old threat. It’s a different model that requires a different defense posture.
If your security strategy is still anchored in endpoint protection and backup restoration, you’re prepared for the version of ransomware that existed five years ago. The current threat is coordinated, multi-vector, and built specifically to overwhelm teams that respond to one thing at a time.
The attack model is well documented. You don’t have to guess what’s coming. You have to build a defense that actually accounts for all of it.
Corero Network Security provides always-on DDoS protection and real-time network traffic analysis that gives security teams the visibility they need to detect and respond to multi-vector attacks before they escalate. Learn more about the Corero Business Continuity Platform.
FAQ
Multi-extortion ransomware is a cyberattack model that uses multiple pressure tactics to compel ransom payment. Rather than relying solely on encryption, attackers combine data theft, public leak threats, DDoS attacks, and in some cases direct pressure on executives or customers to increase the probability of payment.
Single extortion encrypts data and demands payment for the decryption key. Double extortion adds data theft, threatening to publish stolen data if the ransom isn’t paid. Triple extortion layers in a DDoS attack to create simultaneous network disruption. Quadruple extortion adds direct pressure on individuals, including executives, employees, or customers, to accelerate payment decisions.
The full attack chain has compressed significantly. Sophos reports that the median dwell time for ransomware cases in 2025 is just 4 days. ThreatDown by Malwarebytes notes that the entire cycle from initial access through encryption can now occur in hours rather than weeks. Lateral movement breakout times average 48 minutes, with some cases as fast as 51 seconds.
No. According to Sophos’s State of Ransomware 2025 report, the encryption rate has dropped to 50%, its lowest in six years. The proportion of extortion attacks that skip encryption entirely has doubled to 6%. Attackers increasingly find that the threat of data exposure is sufficient leverage without the operational risk of triggering encryption-based detection.
Extremely common. Cyberhaven research found that 96% of ransomware cases investigated included data theft, making double extortion the standard rather than a variant of the core attack model.
A leak site is a public or dark web platform operated by threat actors where stolen data is published after ransom deadlines expire. Data is often released in stages to maintain negotiation pressure. Recorded Future identified over 56 new leak sites in 2024, with more than 3,700 victims listed in just the first half of 2025.
DDoS functions as a pressure amplifier. By creating a network availability crisis on top of encryption and data leak threats, attackers overwhelm response teams and create urgency that pushes victims toward payment. Some ransomware-as-a-service operators now include DDoS capabilities as a bundled affiliate service, according to Vectra AI.
Effective defense requires continuous network visibility to detect lateral movement during dwell time, always-on DDoS mitigation capable of sub-second automated response, data exfiltration monitoring to catch theft before encryption, and incident response playbooks that account for all four layers of the extortion model at once.