Table of Contents
Summary
Multi-vector DDoS attacks deploy dozens of simultaneous attack types — volumetric floods, protocol exploits, reflection amplification, and application-layer hits — while adapting tactics in real time based on how defenses respond. Our SOC recorded a single campaign in August 2025 using over 50 unique vector combinations concurrently. Traditional detection systems that classify before responding can’t keep pace: by the time a vector is identified, the attack has already shifted. Effective defense requires simultaneous detection across all vectors, sub-second response, and testing against realistic multi-vector scenarios rather than single-protocol lab floods.
Multi-Vector DDoS Attacks Don’t Wait for Your Detection System to Catch Up
Most DDoS defenses were designed to handle one thing at a time. That assumption is exactly what attackers are exploiting.
A multi-vector DDoS attack doesn’t arrive as a clean flood you can label, block, and relax. It arrives as TCP SYN variants, UDP floods across multiple port combinations, ACK floods, RST floods, FIN floods, and fragmented UDP, all running at the same time, while the attacker watches your response and adjusts tactics in real time. By the time your detection system finishes classifying what it’s looking at, the attack has already moved on.
That’s not a hypothetical scenario. Our SOC recorded a single campaign in August 2025 that deployed over 50 unique vector combinations concurrently. This is just one attack.

What is a multi-vector DDoS attack?
Single-vector attacks are straightforward: target one protocol or service; flood it until something breaks. A TCP SYN flood, a UDP amplification burst. For a long time, that was the dominant pattern, and defenses got built around it. Classify the attack type, configure a filter, and hold the line.
A multi-vector DDoS attack layers multiple DDoS attack types simultaneously, pulling from volumetric floods, protocol exploits, reflection amplification, and application-layer hits at the same time. The goal isn’t just volume. It’s generating pressure from enough directions that your defense can’t keep up with all of them. While you’re handling one vector, others are doing damage that won’t get classified for another 30 seconds, and by then the attacker has already shifted.
How do multi-vector DDoS attacks work?
It usually starts well before the main event. About a third of the attacks in our 2026 data came in under 1 Gbps, small enough to fly under most alert thresholds. Those aren’t random noise. They’re reconnaissance, mapping how defenses respond before a full campaign launches.
Then the real attack starts, and it doesn’t look anything like the single-vector floods that most detection systems were designed for.
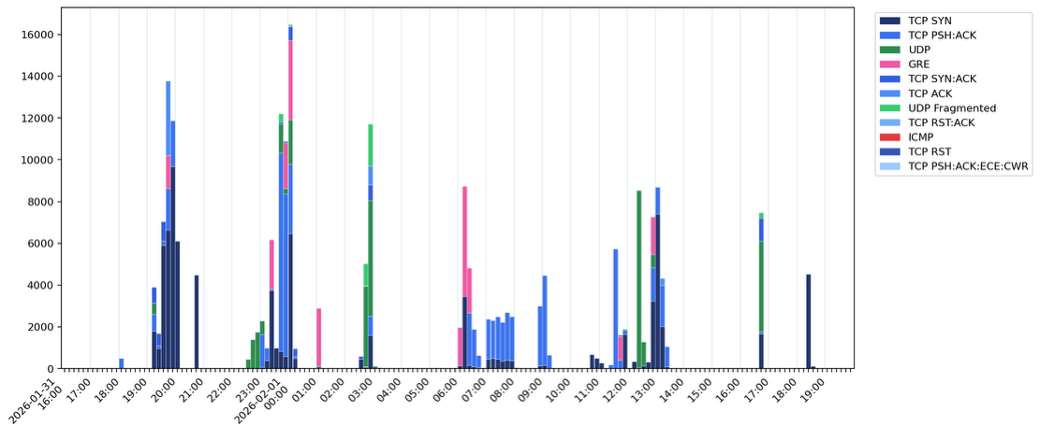
Our SOC introduced the term “chained vectors” last year to describe the emerging pattern: attacks cycling between protocols every 30 to 60 seconds in tight sequence. By 2025, that had graduated from an emerging trend to standard attacker behavior. Reflection-based methods that used to run solo are now frequently deployed in parallel with other simultaneous DDoS attack vectors, and individual reflection volumes have grown over two consecutive years. Stack them together and the compounding effect is what makes them genuinely dangerous.
The bigger shift isn’t the vector count, though. It’s that the attack adapts while it’s running. Attackers watch how your defense responds and change tactics based on what they see. That’s a qualitatively different problem than the one most detection systems were built to solve.
Why are multi-vector DDoS attacks harder to defend against?
Detection systems that classify before they respond have a fundamental timing problem with layered DDoS attacks. When 50 simultaneous DDoS attack vectors are running in parallel and the attacker is adjusting in real time based on your response, the classification window isn’t a minor inefficiency. It’s the attack surface.
There’s a second problem that doesn’t get enough attention: most DDoS defenses have never been tested against anything close to this. Industry-standard testing still relies on single-vector floods, which tells you how a system handles one scenario and almost nothing about how it handles 50 scenarios running at the same time while an attacker adapts to what they observe. The gap between how solutions get tested and how attackers actually operate keeps widening, and it’s entirely in the attacker’s favor.
The sub-1G recon data connects directly to this. When a third of observed attacks are small enough to avoid triggering alerts on most DDoS solutions, and those same low-volume probes are informing the multi-vector campaigns that follow, the small attacks aren’t a separate category of problem. They’re the intelligence-gathering phase that makes complex DDoS attacks more effective when they land.
What this requires from your defense
For a defense to hold against a modern multi-vector campaign, it needs to detect all vectors at the same time rather than processing them sequentially, because anything that classifies first and responds second is handing the attacker a built-in advantage on every exchange. It needs to respond fast enough to actually matter, given that campaigns are now shifting vectors every 30 to 60 seconds. And it needs to have been tested against something that resembles real attacker behavior, not just a single-protocol flood from a lab.
The 50+ vector count from August 2025 isn’t the ceiling. Based on where our SOC sees the data heading, it’s the new floor.
The full campaign data, including the August 2025 and January 2026 incidents, the reflection escalation trends, and what it takes architecturally to handle all of it at once, is in our 2026 Threat Intelligence Report. Read the full report here.
FAQ
A multi-vector DDoS attack layers multiple attack types simultaneously — volumetric floods, protocol exploits, reflection amplification, and application-layer hits — generating pressure from enough directions that your defense can’t keep up with all of them at once.
Single-vector attacks target one protocol and flood it until something breaks. Multi-vector attacks run TCP SYN variants, UDP floods, ACK floods, RST floods, and fragmented UDP all at the same time, while the attacker watches your response and adjusts tactics in real time.
Corero’s SOC recorded a single campaign in August 2025 deploying over 50 unique vector combinations concurrently. Based on current data trends, that’s the new floor — not the ceiling.
Detection systems that classify before they respond have a fundamental timing problem. When 50 vectors are running in parallel and the attacker is adjusting in real time, the classification window isn’t a minor inefficiency — it’s the attack surface.
Attacks cycling between protocols every 30 to 60 seconds in tight sequence. By 2025 this had moved from an emerging trend to standard attacker behavior, with reflection-based methods now frequently deployed in parallel rather than in isolation.
They’re reconnaissance. About a third of attacks in Corero’s 2026 data came in under 1 Gbps — small enough to avoid most alert thresholds — mapping how defenses respond before a full multi-vector campaign launches.
Simultaneous detection across all vectors rather than sequential classification, response speed fast enough to match 30-to-60-second vector cycling, and testing against realistic multi-vector scenarios — not single-protocol lab floods.